Ledger Login: Your Trusted Entry to Crypto Security
Learn how to safely log in to your Ledger wallet, protect your funds, and master crypto asset management with confidence.
What Is Ledger Login?
The Ledger login process is your authentication bridge to Ledger’s world of secure crypto management. It’s the connection point between your physical Ledger hardware wallet—such as the Nano X or Nano S Plus—and the Ledger Live software interface. Together, they form one of the safest ways to buy, store, and manage cryptocurrencies without sacrificing usability or peace of mind.
Unlike traditional platforms that depend on centralized servers, Ledger ensures your private keys remain offline. When you log in, you’re not entering credentials into a website. Instead, you’re confirming access through your physical device, which verifies ownership using a secure element chip.
How to Complete a Ledger Login
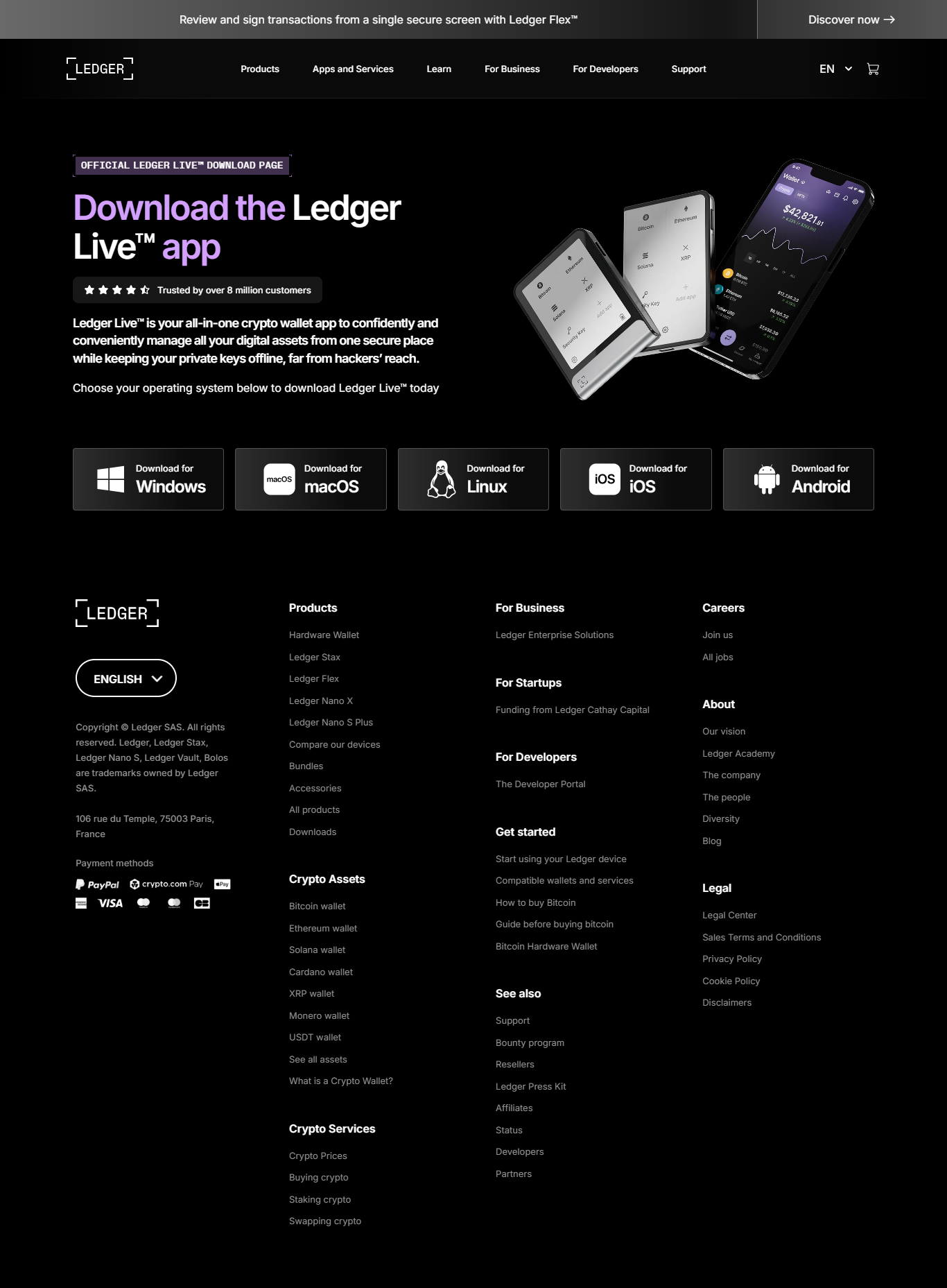
- 1 Download Ledger Live: Get the official Ledger Live app from Ledger’s website to ensure authenticity and security.
- 2 Connect Your Device: Plug in your Ledger Nano or connect via Bluetooth if using a Nano X.
- 3 Enter Your PIN: Authenticate yourself on the device by entering your unique PIN code. This ensures no one else can access your wallet.
- 4 Access Ledger Live: Once verified, your Ledger Live dashboard loads—showing your portfolio, assets, and transaction tools.
Why Ledger Login Is the Gold Standard of Security
Ledger’s login process is purpose-built to eliminate exposure to online vulnerabilities. Each login session is validated by your hardware wallet, where cryptographic signatures are verified offline. Even if your computer is compromised, your assets remain safe.
Ledger’s Secure Element chip, used in passports and credit cards, ensures military-grade protection. This isolation between hardware and network-facing applications makes it virtually impossible for hackers to access your keys.
💡 Pro Insight
Your Ledger device is your digital fortress. Never connect it to unknown computers, and always double-check transaction details directly on the device screen before approving.
Behind the Technology: Ledger Login Security Layers
| Security Layer | Functionality |
|---|---|
| Secure Element Chip | Encrypts and isolates private keys, preventing physical and digital tampering. |
| Firmware Validation | Verifies every software update and blocks unauthorized code installations. |
| Offline Operation | Keeps all sensitive cryptographic operations disconnected from the internet. |
| PIN & Passphrase | Double protection against unauthorized device access. |
Fixing Ledger Login Problems
- Device Not Detected: Switch cables or restart Ledger Live. If using Bluetooth, ensure it’s paired properly.
- Firmware Error: Update the Ledger firmware to the latest version via Ledger Live.
- App Connection Timeout: Reconnect your device and ensure background apps aren’t blocking USB communication.
Ledger Login vs. Other Crypto Wallets
| Feature | Ledger | MetaMask | Trust Wallet |
|---|---|---|---|
| Storage Type | Hardware (Offline) | Software (Online) | Mobile (Online) |
| Security Strength | Very High | Medium | Medium |
| Private Key Exposure | Never | Possible | Possible |
| Offline Accessibility | Yes | No | No |
Ledger Login on Mobile Devices
Ledger Live Mobile allows you to perform the same secure operations as desktop users. Bluetooth connectivity makes it convenient while maintaining the same offline key storage standard. Avoid public networks when logging in, and always verify the pairing code displayed on your device.
🔍 Expert Tip
Enable Ledger’s “blind signing” to verify smart contract transactions directly on your device’s screen, ensuring complete transparency.
FAQs About Ledger Login
1. Can I log into Ledger without the device?
No. The hardware wallet is essential for authentication and transaction approvals.
2. What happens if my Ledger is lost?
Your crypto remains safe. Simply restore your wallet on a new Ledger device using your 24-word recovery phrase.
3. Is Bluetooth login secure?
Yes. Ledger devices use end-to-end encryption for Bluetooth, so your private data remains isolated.
“Every Ledger login is a step toward total financial sovereignty—secure, private, and under your control.”
Conclusion: Ledger Login Redefines Crypto Security
The Ledger login system sets the bar for digital asset safety. It merges robust cryptography with intuitive usability, empowering users to manage crypto securely without relying on third parties. With every login, you’re not just accessing your wallet—you’re reinforcing your digital independence. Protect your keys, trust your hardware, and embrace the freedom that true self-custody brings.